How to Secure AI Generated Code: 5-Step Playbook for Solo Devs [2026]
![How to Secure AI Generated Code: 5-Step Playbook for Solo Devs [2026]](/_next/image?url=https%3A%2F%2Fimages.unsplash.com%2Fphoto-1526374965328-7f61d4dc18c5%3Fw%3D1200%26h%3D630%26fit%3Dcrop&w=3840&q=75)
How to Secure AI Generated Code: 5-Step Playbook for Solo Devs [2026]
You just spun up a fully functional SaaS MVP in three days using Cursor, Claude Code, or whatever AI agent is trending this week. You feel like a god. You're ready to launch on Product Hunt, collect Stripe payments, and watch the MRR roll in.
Stop. Do not hit deploy.
The same AI tools giving you superhuman coding speed are simultaneously arming malicious bots to tear your app apart. You are shipping faster than ever, but you are also shipping invisible backdoors. If you don't know how to secure AI generated code, your launch day is going to turn into a nightmare.
Here is exactly what's happening in the shadows of the indie hacker ecosystem, and the 5-step playbook you need to lock down your codebase before you go live.
TL;DR
- AI agents write code that works, not code that is secure.
- Automated AI scanners are crawling the web specifically looking for boilerplate AI vulnerabilities.
- Rule 1: Never trust AI with authentication or Stripe webhooks. Code those by hand or heavily review.
- Rule 2: Assume all AI-generated database queries are vulnerable to injection unless explicitly parameterized.
- Rule 3: Implement aggressive rate limiting on day one. AI bots will spam your un-secured endpoints.
- Fight fire with fire: run automated security scanners over your AI code before pushing to production.
The New Reality: AI Builds Fast, AI Breaks Faster
Let's get one thing straight: AI coding agents are the greatest multiplier for solo founders in the history of software. What used to take a team of three engineers a month can now be done by one guy on a weekend fueled by cold brew and clever prompts.
But there's a dark side. As you use AI to build, attackers are using AI to break.
Recent reports from threat intelligence firms highlight a massive spike in "AI-enabled vulnerability scanning." In the old days, a hacker had to manually probe your site or run clunky, noisy scripts to find an opening. Today, they deploy autonomous LLM agents that crawl your freshly deployed Vercel app, read your public-facing JavaScript, infer your backend architecture, and silently test for the exact vulnerabilities that AI coding assistants are famous for generating.
We are staring down the barrel of a "SaaS-pocalypse." A reality where thousands of indie hackers deploy similar, slightly flawed boilerplate code, creating a massive, standardized attack surface.
Why Your MVP is a Sitting Duck
AI models like GPT-4, Claude, and whatever powers your IDE are trained on massive datasets of public code. A lot of that code is old. A lot of it is bad. And almost none of it was written with modern security context for your specific application.
When you ask an AI to "build a user login flow with Node and Express," it prioritizes getting you a working result. It wants to show you a functional UI with a success message. It does not prioritize:
- Salting and hashing passwords correctly (it might use MD5 if you don't watch it).
- Setting Secure and HttpOnly flags on session cookies.
- Implementing CSRF tokens.
- Rate-limiting the login route to prevent brute-force attacks.
The AI gives you the happy path. The hacker's AI looks for the unhappy path.
If you are just copy-pasting code blocks or letting an agent write and commit directly to your repo without a security review, you are essentially leaving the front door unlocked and putting a neon sign on your house that says "Free TVs."
Want more hard-hitting truths about building SaaS? We send tactics like this daily to 10,000+ indie hackers. Join IndieRadar — it's free.
The 5-Step Playbook to Secure AI Generated Code
You don't need a dedicated security team. You just need to be smart and methodical. Here is the 5-step playbook to secure AI generated code before your users (or hackers) touch it.
Step 1: Nuke Default Configurations
AI agents love default configurations. They will generate boilerplate setup files that use default ports, default database names, and weak, hardcoded secret keys like JWT_SECRET=supersecretkey123.
The Fix: Before you deploy, audit every single configuration file.
- Move all secrets to
.envfiles and ensure.envis in your.gitignore. - Rotate any API keys or secrets the AI generated during the testing phase.
- Never use default database table names for sensitive data if you can avoid it. Make the automated scanners work for it.
Step 2: Manually Wire the Money & Auth Paths
There are two areas of your app where you cannot afford a single mistake: Authentication and Billing.
If an AI generates a quirky bug in your CSS, your button looks weird. If an AI generates a quirky bug in your Stripe webhook handler, someone upgrades to your $99/mo Pro plan for free, or worse, accesses another user's billing portal.
The Fix: Do not let the AI drive blind here.
- If you use an AI to generate auth, read every single line. Better yet, use established, battle-tested libraries like Auth.js (NextAuth), Supabase Auth, or Clerk. Do not let the AI write custom JWT verification logic from scratch.
- For billing, rely entirely on Stripe's official documentation. If you ask an AI to write a webhook handler, manually verify that it is actually checking the Stripe signature. A common AI hallucination is to write a webhook handler that blindly accepts any POST request and updates the user's database record.
Step 3: Enforce Rate Limiting Before Day 1
AI-generated APIs almost never include rate limiting by default. Why would they? The AI is trying to get the feature working, not protect it from a DDoS attack.
Without rate limiting, a malicious AI bot can hit your /api/signup or /api/reset-password endpoint 10,000 times a minute. Best case, it crashes your server. Worst case, it costs you $500 in transactional email fees via Resend or SendGrid before you even wake up.
The Fix: Implement global rate limiting on your API.
- If you are on Vercel or Cloudflare, use their built-in edge rate limiting.
- If you are running a custom Node server, add
express-rate-limit. - Be especially aggressive on unauthenticated routes (login, signup, forgot password). Limit these to 5-10 requests per IP per minute.
Step 4: Validate Everything on the Backend
The biggest trap indie hackers fall into is trusting the frontend. AI agents are great at adding required attributes to HTML forms or writing Zod schemas for client-side validation.
But hackers don't use your frontend. They hit your API directly using Postman or automated scripts. If your backend blindly trusts the data coming in, you are open to SQL injection, NoSQL injection, and Cross-Site Scripting (XSS).
The Fix: Assume all incoming data is malicious.
- Never concatenate strings to build database queries. Always use an ORM (like Prisma or Drizzle) or parameterized queries. The AI might try to save time by writing
db.query("SELECT * FROM users WHERE email = '" + req.body.email + "'"). That is a death sentence. - Re-validate everything on the server. If you use Zod on the frontend, import that same Zod schema on the backend and parse the
req.bodybefore doing anything else.
Step 5: Fight AI with AI (Use Scanners)
You used an LLM to write the code. Now use an LLM to audit it.
You can't catch everything manually. As a solo dev, your time is better spent talking to customers and marketing your product. Let specialized security tools do the heavy lifting of code review.
The Fix: Integrate automated scanning into your workflow.
- Run GitHub Advanced Security or Snyk on your repository. These tools are specifically trained to look for the exact vulnerabilities that AI agents tend to introduce.
- Before a major feature launch, copy the critical backend files, paste them into a fresh Claude or GPT-4 prompt, and ask: "Act as an expert penetration tester. Find every security vulnerability in this code. Look for injection flaws, broken access control, and edge-case exploits. Do not rewrite the code, just list the vulnerabilities and how to exploit them."
Real-World (Hypothetical) Nightmares
To drive this home, let's look at what actually happens when you don't secure AI generated code.
The "Admin by Default" Exploit:
Let's say you ask Cursor to build a user management dashboard. The AI creates a middleware that checks if a user is an admin. It looks like this: if (req.user.role === 'admin' || req.headers['x-admin-bypass'] === 'true') { next(); }. The AI added a testing bypass flag and forgot to remove it. A scanner finds this header in 5 seconds. Your entire database is now public.
The IDOR Disaster:
You build a SaaS where users can download their invoices. The AI writes an endpoint: /api/invoices/[id]. It checks if the user is logged in, but it forgets to check if the invoice ID actually belongs to that specific user. An attacker simply writes a script to iterate through IDs 1 to 10,000, downloading every single customer invoice, including their names, addresses, and billing details. This is an Insecure Direct Object Reference (IDOR), and AI agents write them constantly.
Conclusion: Build Fast, Don't Build Fragile
AI coding agents are the cheat code to indie hacking in 2026. They allow you to turn ideas into revenue at a speed that was impossible five years ago.
But you cannot outsource your brain. The AI is a junior developer on hyper-speed. It will write 10,000 lines of code without complaining, but it will also leave the stove on, the front door open, and the keys in the ignition.
By applying this 5-step playbook, you put the necessary guardrails in place. You can keep your shipping velocity high without risking your reputation, your users' data, or your MRR. Secure your AI generated code, and then get back to shipping.
FAQ
Can I just use AI to find its own security bugs? Yes, but you have to prompt it specifically for security. If you just ask "is this code good?", it will look at performance and readability. You must explicitly tell the AI to act as a penetration tester and look for vulnerabilities.
Which AI agent writes the most secure code? None of them are perfect. Claude 3.5 Sonnet generally has better reasoning for complex logic and catches more obvious flaws than GPT-4o, but you still cannot trust any of them blindly. The security depends on your prompts and your manual review.
Are built-in frameworks like Next.js secure by default? Frameworks provide tools, but they don't prevent bad logic. Next.js handles route protection well, but if your AI writes a server action that updates the database without checking the user's ID, the framework won't save you.
That's it. If you're serious about shipping secure, profitable SaaS products without wasting time, we send stuff like this daily. Join IndieRadar — it's free.
More in SaaS Tactics Series
Don't miss these related deep dives.
![The TikTok Method: How to Find Viral App Ideas Every Day [2026 Guide]](/_next/image?url=https%3A%2F%2Fvspskxbwtvwkwolfsiil.supabase.co%2Fstorage%2Fv1%2Fobject%2Fpublic%2Fposts_cover_images%2FTwitter%2520post%2520-%252026.png&w=3840&q=75)
The TikTok Method: How to Find Viral App Ideas Every Day [2026 Guide]
Stop overthinking app ideas. Use TikTok trends, search insights, and competitor analysis to find validated ideas daily.
![How to Build an AI Micro-SaaS for "Meeting Fatigue" in 2026 [Playbook]](/_next/image?url=https%3A%2F%2Fimages.unsplash.com%2Fphoto-1517048676732-d65bc937f952%3Fw%3D1200%26h%3D630%26fit%3Dcrop&w=3840&q=75)
How to Build an AI Micro-SaaS for "Meeting Fatigue" in 2026 [Playbook]
Synchronous meetings are killing productivity. Here is the exact blueprint to build, launch, and scale an AI micro-SaaS that cures meeting fatigue for remote teams.

Profitable AI Micro-SaaS Ideas in 2026: Stop Building ChatGPT Wrappers
The market for generic AI tools is dead. Here’s how indie hackers can print money in 2026 by targeting hyper-specific niches, plus 5 actionable ideas you can launch this weekend.

If I Had to Start a SaaS From Scratch in 2026: A Blueprint for Indie Hackers
The exact 6-step game plan to start a SaaS from zero in 2026. Stop building first. Start with the audience, build a 7-day MVP, and launch small.
![The Multi-Product Playbook: How to Build a Portfolio of Apps That Print Money [2026 Guide]](/_next/image?url=https%3A%2F%2Fvspskxbwtvwkwolfsiil.supabase.co%2Fstorage%2Fv1%2Fobject%2Fpublic%2Fposts_cover_images%2FTwitter%2520post%2520-%252031.png&w=3840&q=75)
The Multi-Product Playbook: How to Build a Portfolio of Apps That Print Money [2026 Guide]
Stop betting everything on one app. Here's the step-by-step playbook for building a portfolio of small software products that cross-sell and compound.
![GEO for SaaS: The 5-Minute Playbook to Get AI to Recommend Your Product [2026 Guide]](/_next/image?url=https%3A%2F%2Fvspskxbwtvwkwolfsiil.supabase.co%2Fstorage%2Fv1%2Fobject%2Fpublic%2Fposts_cover_images%2FTwitter%2520post%2520-%252023.png&w=3840&q=75)
GEO for SaaS: The 5-Minute Playbook to Get AI to Recommend Your Product [2026 Guide]
Learn how to optimize your SaaS for ChatGPT, Perplexity, and Claude in under 5 minutes. Copy-paste code included.
![Open Source Marketing Playbook for Indie Hackers [2026 Guide]](/_next/image?url=https%3A%2F%2Fvspskxbwtvwkwolfsiil.supabase.co%2Fstorage%2Fv1%2Fobject%2Fpublic%2Fposts_cover_images%2FTwitter%2520post%2520-%252018.png&w=3840&q=75)
Open Source Marketing Playbook for Indie Hackers [2026 Guide]
Open source is the best free marketing channel for bootstrapped founders in 2026. Here's the full playbook to turn GitHub into a growth engine.
![The 2-Hour Daily Routine That Beats Building More Features [2026 Indie Hacker Playbook]](/_next/image?url=https%3A%2F%2Fvspskxbwtvwkwolfsiil.supabase.co%2Fstorage%2Fv1%2Fobject%2Fpublic%2Fposts_cover_images%2FTwitter%2520post%2520-%252017v2.png&w=3840&q=75)
The 2-Hour Daily Routine That Beats Building More Features [2026 Indie Hacker Playbook]
Stop hiding behind code. Here's the exact 2-hour daily routine that scales SaaS faster than any feature ever will.
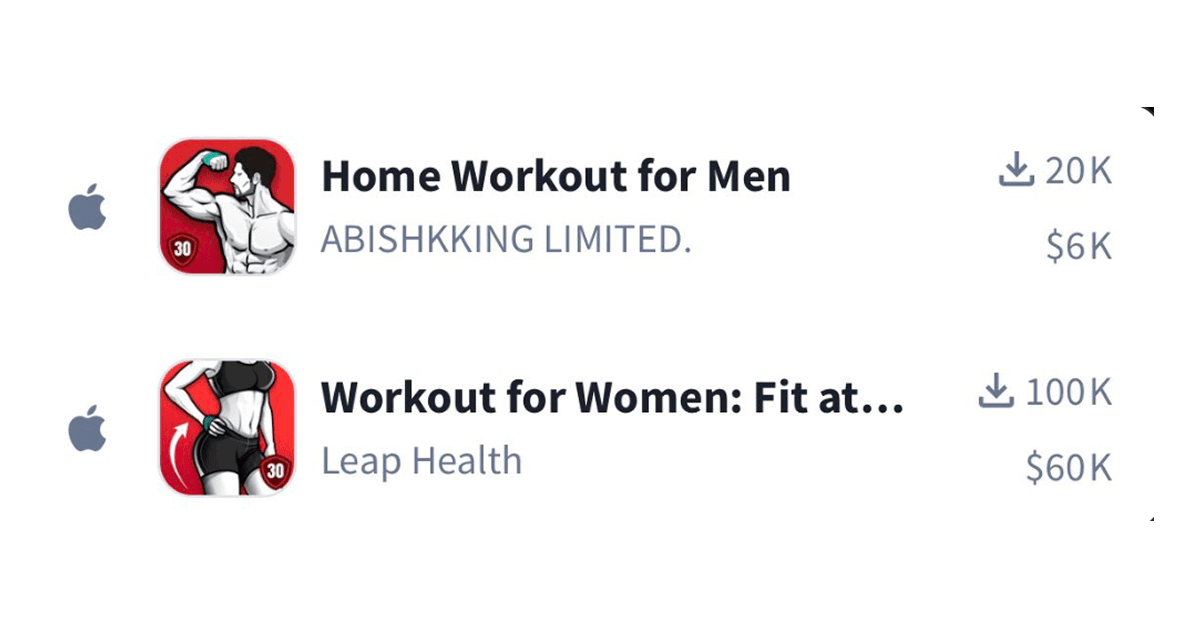
The "Pink" Strategy: Why Building Apps for Women is the Cheat Code of 2026
Men want free tools. Women pay for value. Here's the data-backed strategy indie hackers are using to 10x revenue by pivoting from "generic" to "female-focused."
![Why Every Successful App Has a Mascot Now [2026 Guide to Character-Driven Design]](/_next/image?url=https%3A%2F%2Fimages.unsplash.com%2Fphoto-1551651653-c5186a1fbba2%3Fw%3D1200%26h%3D630%26fit%3Dcrop&w=3840&q=75)
Why Every Successful App Has a Mascot Now [2026 Guide to Character-Driven Design]
Mascots are taking over top-grossing apps. Here's why character-driven design converts better and how to add one to your product.
IndieRadar Team
Daily newsletter for indie hackers. We analyze 10,000+ tweets and deliver the signal.
Read Next
![The Multi-Product Playbook: How to Build a Portfolio of Apps That Print Money [2026 Guide]](/_next/image?url=https%3A%2F%2Fvspskxbwtvwkwolfsiil.supabase.co%2Fstorage%2Fv1%2Fobject%2Fpublic%2Fposts_cover_images%2FTwitter%2520post%2520-%252031.png&w=3840&q=75)
The Multi-Product Playbook: How to Build a Portfolio of Apps That Print Money [2026 Guide]
Stop betting everything on one app. Here's the step-by-step playbook for building a portfolio of small software products that cross-sell and compound.
Read article
If I Had to Start a SaaS From Scratch in 2026: A Blueprint for Indie Hackers
The exact 6-step game plan to start a SaaS from zero in 2026. Stop building first. Start with the audience, build a 7-day MVP, and launch small.
Read article
Profitable AI Micro-SaaS Ideas in 2026: Stop Building ChatGPT Wrappers
The market for generic AI tools is dead. Here’s how indie hackers can print money in 2026 by targeting hyper-specific niches, plus 5 actionable ideas you can launch this weekend.
Read article